Anomaly Intrusion Detection System Diagram Anomaly Based Ids
Classification of anomaly-based intrusion detection techniques Intrusion detection module operation diagram. it performs the following Detection intrusion anomaly
Anomaly Detection System Design. | Download Scientific Diagram
Detection anomaly intrusion Intrusion detection anomaly Anomaly detection
2: anomaly-based ids
Anomaly intrusion detection technique[pdf] a survey on anomaly and signature based intrusion detection Anomaly analyzer system architecture and data flow diagram.Anomaly based ids examples.
Anomaly intrusionAnomaly-based intrusion detection system Anomaly detector process in near-real-timeAnomaly-based intrusion detection system.

Anomaly detection system – elfisystems
Anomaly intrusion ids proposedAnomaly based ids examples Anomaly-based intrusion detection systemSequence diagram of anomaly detection system..
Passive deployment of network‐based intrusion detection systemFigure 3 from review on anomaly based network intrusion detection Anomaly detection technique for intrusion detection figure 2 depictsIds anomaly detection intrusion analyzer proposed hybrid.
(pdf) anomaly intrusion detection system based on unlabeled data
Building smart intrusion detection system with opencv & python什么是ids(intrusion detection system)入侵检测系统?都有哪些类型?nids、hids、基于特征、基于异常等 Based detection anomaly system intrusion network intechopen figureWhat is an intrusion detection system?.
Basic idea of a cooperative anomaly and intrusion detection systemIntrusion detection ids system snort systems work does server types linux security computer intrusions install activities Intrusion & anomaly detectionAnomaly detection system design..

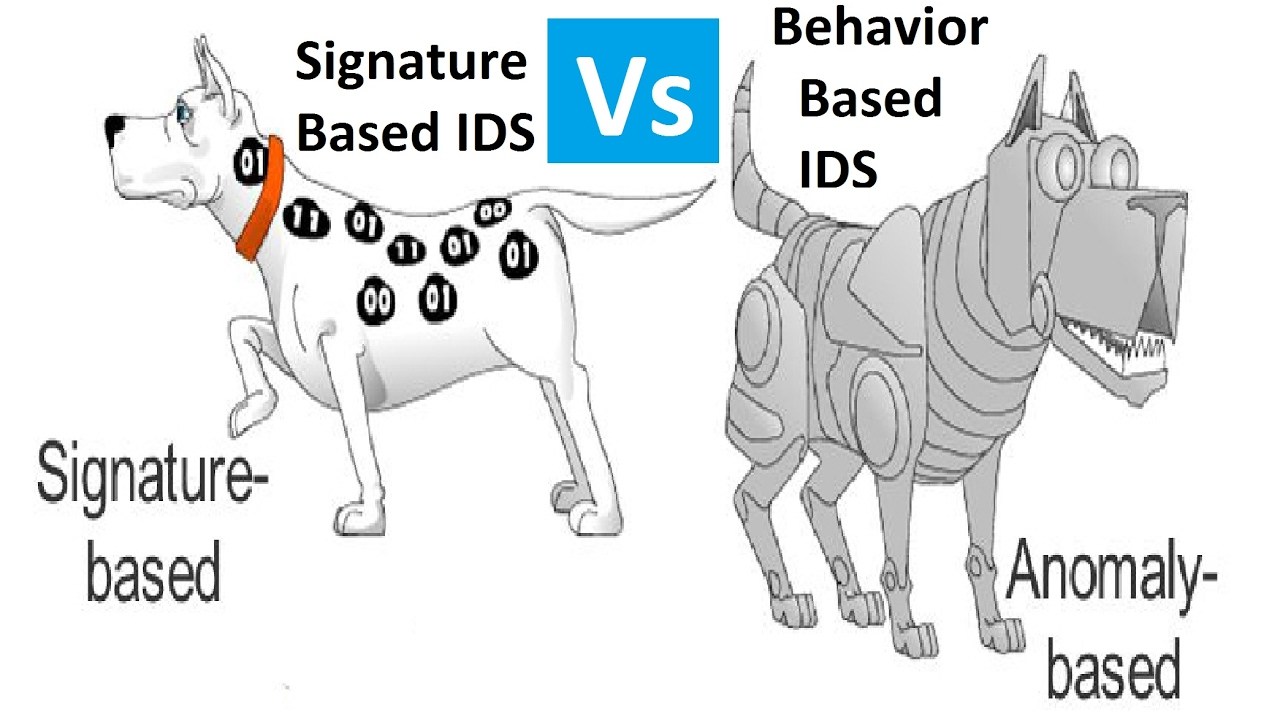
Signature based ids || anomaly based ids
Anomaly proposedAnomaly-based intrusion detection system Training phase of an anomaly detection system.Computer security and pgp: what is ids or intrusion detection system.
Anomaly based intrusion detection systemAnomaly detection system: proposed architecture. Anomaly-based intrusion detection systemIntrusion detection performs functions.

Figure 1 from review on anomaly based network intrusion detection
The architecture of the proposed anomaly-based intrusion detectionDetection intrusion anomaly based system systems Anomaly intrusion detection system [14]..
.


Anomaly-based intrusion detection system | Download Scientific Diagram

Anomaly Based Intrusion Detection System
Anomaly-based intrusion detection system

Figure 3 from Review on anomaly based network intrusion detection

Anomaly Detection Technique for Intrusion Detection Figure 2 depicts
Anomaly Detection System Design. | Download Scientific Diagram
Intrusion detection module operation diagram. It performs the following